Understanding the Critical Role of a VPN in Modern Digital Life
In an era where online risks are growing, securing your private data has never been more vital. A VPN encrypts your digital communications, ensuring that cybercriminals, ISPs, and unauthorized users cannot observe your browsing habits. Whether you’re connecting to public Wi-Fi at a hotel or managing private records, a VPN acts as an invisible barrier against security leaks.
Individuals overlook the threats of unsecured networks, exposing their banking information, passwords, and chat records. By channeling your connection through secure servers, a 快连vpn masks your digital location and real-world position, making it extremely difficult for tracking agencies to identify you.
Selecting the Ideal VPN for Your Gadget: A Comprehensive Comparison
Picking the right VPN solution depends on your specific needs and OS. For PC owners, look for intuitive designs, fast servers, and advanced security. Mac users should prioritize flawless operation with Apple ecosystems, while tech-savvy users may favor flexible controls.
Mobile device users must select VPNs with mobile-optimized applications that minimize energy usage and bandwidth usage. Cross-platform compatibility is critical if you frequently switch between desktops, tablets, and handsets. Always confirm that your VPN supports latest protocols like OpenVPN for peak efficiency.
Step-by-Step Guide to Downloading a VPN on PC Systems
To begin, access the service’s homepage using a trusted browser. Identify the get started area and select the PC-friendly edition. Post-download, execute the executable and follow the installation wizard.
While configuring, customize options like automatic startup and protocol selection. Enable the network lock feature to halt breaches if the VPN loses signal. Lastly, sign in with your username and password and connect to a location of your choice.
Optimizing VPN Usage on Mac Systems
Mac systems offers integrated features for VPNs, but third-party apps often provide superior capabilities. After downloading, place the VPN software to your software library. Launch the app and key in your subscription details to enable the service.
Customize configurations such as protocol selection and geographical preferences. Enable split tunneling to channel certain programs through the 快连手机版 while permitting others to use your standard internet. For extra security, integrate your VPN with Firewall tools to block malware and fraudulent links.
Securing Tech-Advanced Devices with a VPN
Linux users often prefer VPNs that work with command-line interfaces. Start with, updating your package manager to guarantee compatibility to the updated applications. Use CLI instructions to install the VPN service, adhering to manuals provided by your service.
Adjust connection parameters to automate VPN connections during boot-up. Advanced users can embed security policies to restrict insecure connections. Frequently inspect records to detect suspicious activity and patch your VPN tool to resolve security gaps.
Protecting Smartphones with VPNs on Google’s OS and iOS
Mobile devices are prime targets for data breaches due to their permanent internet access. Download your VPN app from the Google Play Store to avoid malicious software. Open the app, sign in, and choose a location nearby for faster speeds.
Activate tools including malware filtering to boost your internet usage. Set up the VPN to automatically link when accessing website unsecured networks. For Apple mobile devotees, enable Always-On VPN in configuration menus to sustain privacy even if the app terminates.
Advanced VPN Features to Boost Your Security
Today’s services provide cutting-edge options that exceed basic encryption. A emergency stop stops all internet traffic if the VPN drops, avoiding data exposure. Multi-hop directs your connection through two or more locations, masking your digital trail to a greater extent.
Threat detection systems eliminate annoying pop-ups and prevent risky domains. Selective routing lets you decide which apps use the VPN, balancing speed and protection. For teams, fixed locations and account control facilitate encrypted communication.
Addressing Common Myths About VPNs
Even with their popularity, many users misinterpret how VPNs work. A common fallacy is that VPNs entirely hide your online activity. While they mask your location, browser fingerprints can still leak your identity. Additionally, not all VPNs follow zero-data retention rules, so examining your provider’s policies is vital.
A second fallacy is that VPNs dramatically reduce internet speeds. While encryption creates overhead, premium services lessen this impact with optimized servers. Lastly, no-cost services often undermine privacy by selling user data or serving intrusive ads.
Future-Proofing Your Digital Life with a VPN
As cyber threats advance, remaining secure requires proactive measures. Upcoming innovations like advanced algorithms could threaten current protection methods, making it essential to opt for VPNs committed to enhancing their networks. Pairing a VPN with supplementary measures like secure storage and biometric checks builds a multi-layered defense framework.
Regulators worldwide are strengthening data privacy laws, and a VPN guarantees you adhere with these rules. Whether you’re watching videos, engaging in eSports, or conducting business, a VPN remains an indispensable tool for traversing the digital world safely.
 Jason J. Richter Then & Now!
Jason J. Richter Then & Now! Seth Green Then & Now!
Seth Green Then & Now! Barry Watson Then & Now!
Barry Watson Then & Now! James Van Der Beek Then & Now!
James Van Der Beek Then & Now!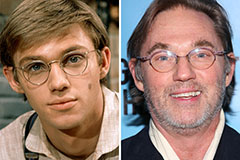 Richard Thomas Then & Now!
Richard Thomas Then & Now!